WebSpy analyze and report on different types of log files, from different types of network and security devices (such as web servers, web proxy servers, email server, event logs, firewalls, switches, routers, and spam and virus application), taking raw data and converting it into meaningful and actionable information.
We take great pride in this versatility and the fact that our software is virtually vendor neutral, or universal. At the time of writing our software support 128 different vendors, and more than 250 log file formats. But what does all this actually mean? What’s all this log file format gibberish and why is better to use a universal log file analyzer than a reporting solution that can only analyze a limited set of log files?
Let’s break it down…
What is a Log File?
A log file is a set of data that is automatically created and maintained by a security or network device of activity performed by it.
Web proxy servers maintain log files listing details on every request, from outgoing traffic, made to the proxy server – who is accessing external sites, what sites are being accessed, when the sites were accessed, what page or search phrase referred the user to the sites, and the type and size of data downloaded from the sites. Email servers store log files containing data about the sender, the receiver, timing of delivery or receipt, subject line, and size of attachment. Firewalls, and other security devices, normally contain data about network activity and the external and internal traffic that has been blocked or filtered.
Log files contains bundles of information and are usually not very structured or easy to decipher. Here’s what a log file can look like:
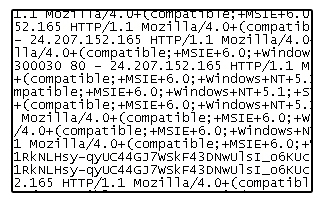
Can you see the need for a log file analyzer?
Who are the Network and Security Device Vendors?
There’s a bunch of them to say the least. A recent WebSpy customer survey showed that Microsoft, Novell, Squid, IronPort, Blue Coat and CheckPoint were the top vendors whose products our clients wanted to analyze.
Checkout the whole list (128) of vendors we support at http://www.webspy.com/resources/logformats.aspx
What is a Log File Format?
When we state we can analyze more than 250 different log file formats we take into account the different log files formats produced depending on the vendors’ product, product version and log type
For example: Microsoft develops products such as Exchange, IIS, Proxy Server and ISA Server. ISA Server comes in different versions (2000, 2004 and 2006). Each version can log and store different types of log files (file, MSDE Database and SQL Database). So, ISA Server MSDE Database 2004 is one log file format we support, ISA Server file 2000 is another.
Benefits of a Universal Log Analyzer
The 250 something log file formats WebSpy analyze and report on are simply the most common ones. It is very rare that we come across a client who need to analyze a log file that is not already on our list of supported log files. On the odd occasion this does occur, the client can simply request support for their specific log file format, our developers work their magic and wham – we support one more log file format.
Most competing log file analyzers are hard-coded to analyze a particular log file type. When this is the case their clients will need a different log analyzer to achieve each individual reporting requirement, increasing the time and costs involved to produce all the required reports.
WebSpy’s clients, on the other hand, reap the rewards of using one application to achieve all their reporting requirements, spending less on software maintenance, hardware and administration.
See also:
- More Students Bypassing Schools’ Internet Security
- 3 Simple Reasons Why Resellers Want WebSpy
- WebSpy Partners with Netherlands Distributor Avnet Technology Solutions
- Business benefits from monitoring and reporting on Internet, email and network log files
- How I used log file analysis to safely retire a legacy web site

Leave A Comment